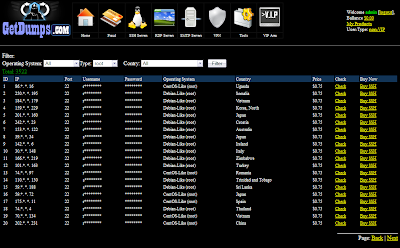
Another (lame) and fake carding shop:
• dns: 1 ›› ip: 94.215.213.31 - adresse: GETDUMPS.COM
Spam:
Dashboard:
Paypal:
Dumps:
Cards:
Ebay:
Western Union transfer:
SSH Server:
RDP Server:
SMTP:
VPN:
Tools:
cPanel:
c99 shell:
Balance:
My products:
VIP:
If you try to add funds on the shop with your Liberty reserve account, a script will wipe all your money.
people looking for LR Curl script:
People selling the script on carding forum
Scam site example:
LR Curl script in action, detail of victims are saved into text files
More than 1000 carders got scammed by this, jackpot for the guys behind.
Someone who card:
Declined payement for Avira:
Another guys:
Another..:
Want have fun too ?
http://temari.fr/getdumps.com-users.txt
passwords in plaintext, happy lurking.
Showing posts with label lr. Show all posts
Showing posts with label lr. Show all posts
Sunday, 5 May 2013
getdumps.com Fake Carding shop and LR Curl scam script
Labels:
card,
Carding,
carding shop,
cpanel,
credit card,
Curl,
dumps,
eBay,
getdumps.com,
Hacked,
Liberty Reserve,
lr,
LR Curl scam script,
RDP,
Scam,
SMTP,
SSH,
VPN,
Western Union,
WU
Monday, 29 April 2013
Fake carding shops
Nothing new here, just three forums used to scam stupid people like carders.
It's always the same method: advertising via spam and to view the content you must pay a fee.
Our first forum is a phpbb with fake statistic.
• dns: 1 ›› ip: 50.7.199.110 - adresse: FORUMSCC.COM
Forum look's huge:
Users are charged a $0.5 LR fee to view forums:
Fake online users:
Second example, fake carding shop:
• dns: 1 ›› ip: 96.125.170.142 - adresse: MARALIMACLASSIC.COM.BR
The captcha is iframed:
When you complete the name field and click login you are redirected always to register.html
The site index is defaced by a random lammer:
register.html
When you click to register you are redirected on a fake Liberty Reserve page:
• dns: 1 ›› ip: 198.24.144.50 - adresse: SCI.LIBIRTYRESERVES.COM
Another fake site, probably do by the same guys:
Mailer:
Some other files found on the compromised server, cPanel bruteforcer:
Another cPanel bruteforcer:
Ac1db1tch3z x86/x64 Linux kernel exploit (EXP/Linux.Small.AU):
The mail lead here:
• dns: 1 ›› ip: 199.79.62.93 - adresse: ZCB.CO.IN
And when you click on register...
• dns: 1 ›› ip: 50.28.73.7 - adresse: SCII.LIBERTYERESERVE.COM
PHP stuff can be found here: http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2410&p=19111#p19111
EXP/Linux.Small.AU here: http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2697#p19112
It's always the same method: advertising via spam and to view the content you must pay a fee.
Our first forum is a phpbb with fake statistic.
• dns: 1 ›› ip: 50.7.199.110 - adresse: FORUMSCC.COM
Forum look's huge:
Users are charged a $0.5 LR fee to view forums:
Fake online users:
Second example, fake carding shop:
• dns: 1 ›› ip: 96.125.170.142 - adresse: MARALIMACLASSIC.COM.BR
The captcha is iframed:
When you complete the name field and click login you are redirected always to register.html
The site index is defaced by a random lammer:
register.html
When you click to register you are redirected on a fake Liberty Reserve page:
• dns: 1 ›› ip: 198.24.144.50 - adresse: SCI.LIBIRTYRESERVES.COM
Another fake site, probably do by the same guys:
Mailer:
Some other files found on the compromised server, cPanel bruteforcer:
Another cPanel bruteforcer:
Ac1db1tch3z x86/x64 Linux kernel exploit (EXP/Linux.Small.AU):
The mail lead here:
• dns: 1 ›› ip: 199.79.62.93 - adresse: ZCB.CO.IN
And when you click on register...
• dns: 1 ›› ip: 50.28.73.7 - adresse: SCII.LIBERTYERESERVE.COM
PHP stuff can be found here: http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2410&p=19111#p19111
EXP/Linux.Small.AU here: http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2697#p19112
Thursday, 20 December 2012
Talking to a FakeAV black processing service
Finding a payement processor for black is complicated and private kind of business because they are connected with banks and real life, in 2011 most of FakeAV program was in difficulty due to the ChronoPay story.
Good example of a know payment processor:
130.185.108.163:
130.185.108.162:
130.185.108.161:
130.185.108.157:
130.185.108.156:
194.54.83.82:
Used by Security Monitor 2012 and many others, landing are still in place:
Let's contact a payement guys:
First approach:
He answered that they work through lithuana bank and want 20% from revenue.
They are not connected with ChronoPay and have just finished a new project (now in test)
One week later:
I asked him about security, trustworthness of the bank, offshore account, type of payments, duration of payments, etc.
He said they can transfer money via LR, WM, Wire Transfer, cash and an offshore is needed to transfer money via wire.
He said the bank knows about malware and won't cooperate with police
He also said that i need hosting and clean domains, then he would give me all instructions to make a payment page.
I've not coded a Fake-FakeAV affiliate but that can be a future project to trap payement processors and fakeav actors.
HS: Thanks for the postcard /a/non, received everything and i still wait 25 dec to unbox the rest, meri kurisumasu to you too (´・ω・`)
Good example of a know payment processor:
130.185.108.163:
130.185.108.162:
130.185.108.161:
130.185.108.157:
130.185.108.156:
194.54.83.82:
Let's contact a payement guys:
First approach:
He answered that they work through lithuana bank and want 20% from revenue.
They are not connected with ChronoPay and have just finished a new project (now in test)
One week later:
I asked him about security, trustworthness of the bank, offshore account, type of payments, duration of payments, etc.
He said they can transfer money via LR, WM, Wire Transfer, cash and an offshore is needed to transfer money via wire.
He said the bank knows about malware and won't cooperate with police
He also said that i need hosting and clean domains, then he would give me all instructions to make a payment page.
I've not coded a Fake-FakeAV affiliate but that can be a future project to trap payement processors and fakeav actors.
HS: Thanks for the postcard /a/non, received everything and i still wait 25 dec to unbox the rest, meri kurisumasu to you too (´・ω・`)
Subscribe to:
Posts (Atom)