And some traps who have do all the magic... i've phished the phisher.
Some phishing pages on a compromised server:
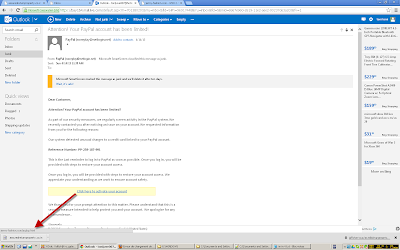
The guys behind these fishs is know as 'Tonix', here is a screenshot of his mail adress:
Here, Tonix test his fake paypal template, the link lead on a phishing redirector.
The server was hacked due to a vulnerability with 'lang_wmps' the hacker have uploaded a well know backdoor: WSO
Paypal Phishing:
After re-hacking the compromised server and changing the pass of the backdoor we got the mail adress:
tonijuve10@inbox.com... let's have a look now:
256 mails (without mails inside the junk folder and deleted folder) this email is used only for his phishing activities.
On the 'sent mail' folder there is mails of 2012 with phished datas.
The case of Phyllis Stevens, datas phished the 14 april 2013:
Phyllis Stevens credit card used to buy a server the 15 april 2013:
Tonix leaved several trace of him, example here testing his phishing page:
Same IP found on access log who connect to the backdoor:
216.104.32.43 is a ExpressVPN IP:
And of course, Tonix use/carded this service:
SQL injection used:
71.187.243.7 is a VPS IP and the user-agent on access logs tell us that he used Havij to exploit the SQL vulnerability:
The phishing spam is also sent from this machine.
Having fun with metasploit and the good MS12-020
not worked here but i should do that more often on carded vps :)
Tonix have access to several compromised VPS, some even warn you:
He have also some compromised POS:
Brute force attack on another compromised server:
Failed exploitation for a plugin who don't exist:
Bank Of America phishing:
The phishing kit used for Bank Of America is even backdoored, did Tonix know that ?
And also $remote = $_POST['REMOTE_ADDR'];
MR.M1ND.php?REMOTE_ADDR=./../../../../../etc/passwd
Paypal and Bank Of America phishings can be downloaded here: http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2431&start=10#p19028
The attacker (91.187.125.189) according to log files used the edit template feature of Joomla to upload a backdoor.
Also seem someone tryed to find a phishing kit archive, here is what i've found inside the log file: http://pastebin.com/XWx8DXuZ
Another example:
Tonix seem Albanian and have did several orders with his real identity.
I've found various SMS in Albanian with his phone number, most of messages are about chilling with friends.
On another email the phone number is the same for shipping information of 'Faton':
Tonix is a big fan of Juventus, some of his passwords are even related to this club.
He have do many sites related to Juventus, like grandejuve.com
A whois give us an ytahoo adress 'rodrigue123456789' registered by Tonix.
On another order, same shipping information:
Beats by dr.dre registration to 'faton':
DHL tracking for a product:
Apple store carding:
Order to Arben (a friend of him?):
Another order to Arben:
Failed order to Adnan:
Although one order seem not carded:
Seems like he's been doing phishing/carding since 2011:
Visual map based on shipping details:
Faton selling stuff, the phone number is the same for carded stuff.
Facebook profile:
I got the confirmation that it's him on facebook via his twitter profile
Same head, same interest in Juventus, same location but the website link have not the same gTLD.
After searching a whois, the email is registered to Toni and registrant details make me think he carded the domain.
He even carded a domain for a member of his family
Anyway with everything here i'm not going to give his details to authority, but he should take care and leave the business, carding and phishing is definitely not for him.















































Awesome work there Steven. More! :-)
ReplyDeleteyou pwnd that guy WAY TO HARD
ReplyDeleteI lol'd...
ReplyDelete))))
ReplyDeletetoo much pwnage for ********!
ReplyDeleteno personal info please
DeleteHe deserves to get punished. People like him cause trouble for so many people. He is lucky because I would send his data to he police to ensure this guy will learn his lection.
ReplyDeleteFranchement à ta place j'aurais disclo le tout.
ReplyDeleteLOLILO
ReplyDeleteHey Steven, i love your research and work
ReplyDeleteI notice you use irc, may i know it to chat more :)
If anything you can contact me here null0x00x@gmail.com
Lol, Nice work :P
ReplyDelete>:p haha tu l'as ruiné! GG
ReplyDeleteHow did you get access to his email?
ReplyDeleteaccording to the map hes in kosovo, not albania
ReplyDeletePutain quelle tanche...
ReplyDeletewow xyli you friggin rock.
ReplyDeleteSo let me get this straight, you are not gonna report this guy, you are just going to pray/hope that he stops scamming innocent people, right?
ReplyDelete@fd to continue what you said: well...that's stupid if you think he's gonna stop... :|
DeleteDAFUQ !!!! .... ;) w
ReplyDeleteHehe, thank you for your time Steven. I had his ip and other evil stuff on our server. I was too busy cleaning the shit, so I bow to you for you effort in gaining the needed information, to bring him to justice.
ReplyDeleteThe sad thing is that I think that the albanian justice department won't do anything against him.
We should punish him in making his life a bit harder when ever he joins the web :)
Knowing how things work around here (the Balkans) I wish you post his real name because I doubt he will get any other punishment. Make him famous :)
ReplyDeleteNice work, but you should report this cunt.
ReplyDeleteSeriously, there's no way this guy is going to stop. He'll change his tactics, operate a little more securely, and be a bit more careful. Turn him in.
ReplyDeleteGood Job.
ReplyDeleteNice work SK
ReplyDeleteIt is great work... Phishers should know that , there are others also who could do this.. Noone is ace....
ReplyDeleteGreat job sleuthing. IMHO you need to report him. He wont stop until he's caught. For you to go this far without reporting him seems like a wasted effort... although fun :)
ReplyDeleteIts easy to find out the real details of this guy from Xyli's details, so any one of us could report him.
ReplyDeleteHAHAHA YOU ARE INCREDIBLE MAN ;)
ReplyDeleteGreat job! I am not the best person online but your work really inspires, keep it up.
ReplyDeleteBelle démonstration. J'adore ton blog, c'est vraiment passionnant.
ReplyDeleteNice Démo. I love your blog, it s very exciting.
wow dis is so extreme..owning...nice1. :D honestly me too do bad stuff..online..but your really good..weldone..
ReplyDeleteГлупав шиптар...
ReplyDeleteHow can you figure out who is trying to fuck me with the paypal western union scam? He thinks everything is good and I don't know what he is trying to do. I have all the emails and his emails. It started from an ad on Kijiji and I have everything from the beginning. THE REAL ANONYMOUS PLEASE HELP ME!!!!
ReplyDelete