Old school malwares are fun especialy 'Acid Drop' a RAT not complicated to use
I've found it by error when i was searching another threat, you can find a description of Acid Drop here: http://www.mcafee.com/threat-intelligence/malware/default.aspx?id=114534
Know as 'BackDoor-ARD' by McAfee, Acid Drop is written in Visual Basic and need MSCOMCTL, MSWINSCK and TABCTL32 to run properly (the joy of vb6).
The Client i've found was packed by PECompact.
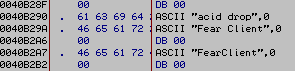
And several weird strings appeared:
Acid Drop seem ripped from 'Fear Client'
So i've searched on Internet and i've found 'Satan' (Another rip?)
Both are similar (Hi Richard):
The two clients have exactly the same features and GUI:
Fun tab:
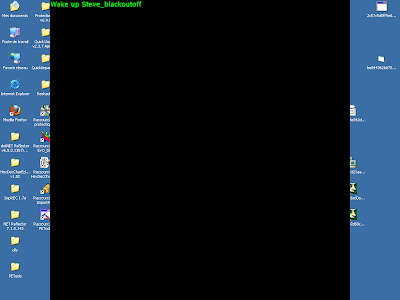
On Satan, the 'matrix' feature seem badly coded
'blackoutoff' appear on dialog without typing it, it's a function inside to remove the black screen after seconds, but bugged.
Acid Drop seem don't have this problem.
Explorer tab:
Info tab:
The 'server.exe' work both for Acid Drop and Satan Client.
Acid Drop MD5: 210712b6923aea4212f4e4bcb47b44aa
Satan MD5: 0f71dc45e3e506553dd4959712a7be9c
Server MD5: 3135c6526e3ca1c1e9b340a3ffb30fa0
Acid Drop compilation timedatestamp: 2004-04-14 20:37:50
Satan compilation timedatestamp: 2002-01-04 21:16:54
Server compilation timedatestamp: 2002-01-04 21:17:23
But there is a problem with Satan:
"Released: May 20 2004"
The description of BackDoor-ARD on McAfee website was added the 2004-04-20 and they don't speak of Satan, the signature was added the 2003-03-19 on McAfee engine, so if we refers to the timestamp Satan was undetected by McAfee for 1 year ?
The server don't have registry persistence and the process can be simply killed with task manager.
It's really a simple RAT, that can be the cause on why McAfee set time.
What's others guys says on FearDroor ?
Paretologic:
C'mon damage level and distribution are low.
spywareviruscleaner.com (affiliate site for PCSafeDoctor)
Total bullshit, and what the fuck is XTray.exe ?
Symantec was more fast to detect it
And who are the bad guys who still don't detect Feardoor ?
According to VirusTotal we have 6 winners.
• ByteHero
• CAT-QuickHeal
• eSafe
• SUPERAntiSpyware
• TotalDefense
For SUPERAntiSpyware you can read this on the footer of the official website:
The threat is probably too old for them, for others companies i don't know.
They have not added a date when they started and i'm bored to search.
Connection to the server using the port 8811
When the server receive a command
The received command here is 'www www.acid-alchemy.com' for a webpage popup try.
The command is parsed to get just 'www'
And compared to other know commands to find the action to do
List of commands:
Yes, it's a good example of 'hard-coded' RAT
StrCmp.. StrCmp everywhere.
And when it finaly get it, the command is parsed again but this time to get URL
The sub-routine just do 'open URL' with shellexecuteA, a vb6 classic.
Acid Drop source code was probably released
On web-archive we can found some captures of acid-alchemy.com
A leet NukedKlan CMS and a lot of Yahoo booters.
Fu*$#ing pi*% news:
Ho no... McAfee and some others identify the trojan.
WhAt ThE f^¤cK
Hackerz-inc was pretty simple:
I miss the 2004 keyboard cowboys.





























I knew "Acid" aka Yaz. Good guy. He and Berry split up and he fell off. I still talk to Berry from time to time. She's a great girl.
ReplyDelete