Another interesting treat today.
A ransomware who XOR the first byte of some formats
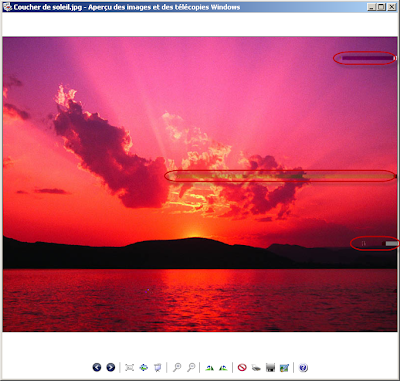
If you have your wallpaper changed by this:
You should worry :)
--------------------------
This trojan ransom ( MD5: 359d532274b3a44a8f9bacb942c478d2 ) xor some of your datas.
To recovers your datas, infected users need to payd a ransom (fileunblock@gmail.com - xddd.66ghz.com).
Setup.exe on VT: https://www.virustotal.com/file-scan/report.html?id=5706be5130b214c9885d4098e1b6533c285d9a35c2e923cfed7d73048d12a4e1-1303751832
So how the infection work ?
let's see that.
The infection is composed of two Delphi binary who are exactracted and run by Setup.exe (Setup.exe is a file powered by Smart Install Maker v5.02).
1 File (named svchost.exe) Will crypt your datas and the second (named also svchost.exe) will lock your screen if you attempt something for stop the file
For example if an antivirus is detected or if you browse the website 'VirusTotal' your pc will be locked.
We will see this file later, let's see the one who xor your file.
A file named инфа.txt is created:
все ваши файлы заблокированы посетите сайт: http://xddd.66ghz.com/
вам присвоен id 215 cообщите его на почту указанную на сайте
вам присвоен id 215 cообщите его на почту указанную на сайте
Infection locs:
%Programs%\Startup\
%ProgramFiles%\KOPPEKTOP\Soft\
C:\ttt.jpg
xddd.66ghz.com Website capture (domain shutdown requested):
---
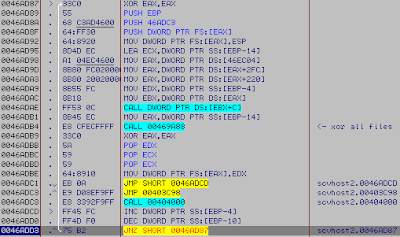
Firstly the ransomware will crawl these drives:
C:\
D:\
E:\
F:\
In each drive it will list your datas and compare the extention (for know wich files the ransomware will xor)
'Attacked' extentions list:
List:
*.JPG
*.DOC
*.RTF
*.XLS
*.ZIP
*.3GP
*.RAR
*.7Z
*.DOCX
*.MP4
*.PPS
*.DPR
*.POT
*.DOT
*.HTM
*.PDF
*.ISO
*.PPSX
*.EML
*.AVI
*.PPTX
*.HTML
*.TIF
*.DOC
*.RTF
*.XLS
*.ZIP
*.3GP
*.RAR
*.7Z
*.DOCX
*.MP4
*.PPS
*.DPR
*.POT
*.DOT
*.HTM
*.ISO
*.PPSX
*.EML
*.AVI
*.PPTX
*.HTML
*.TIF
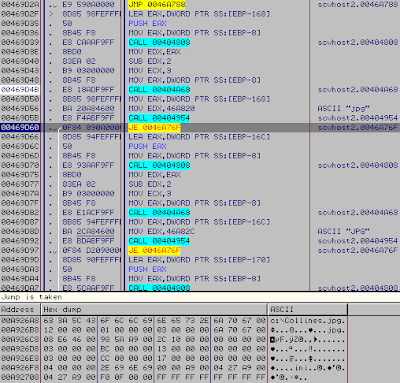
When done, it start to xor all files he have found previously into this loop:
Detail of the procedure:
Take the first byte of your file:
Then it XOR the byte with 4B (41 XOR 0A)
And do a WriteFile for save the change, then it proceed to the next file.
When all files are Xored, it change your wallpaper by 'ttt.jpg' (what a wonderful wallpaper heh...)
0046AF7C=scvhost2.0046AF7C (ASCII "c:\ttt.jpg")
EDX=0012FDBC
EDX=0012FDBC
Then it create a .BAT file for his auto-delete (like that, no proof about the file who xored your datas)
Then ExitProcess (ByeBye)
That all for the first scvhost.exe of 643 Kb.
Now for the second file: the scvhost.exe of 378 Kb
This file is just a protection for the previous one, like i've said
It just do a loop and compare the title of all opened windows
If a windows contain one of these word:
The application will appear maximized on your screen and alway at the top
Tricks like ALT+F4, ALT+TAB, CTRL+ALT+DEL will not work for move the maximized windows.
As you can see here, i've tryed to go on the site 'VirusTotal' and suddenly this grey window appear.
So that all for the second file, just a protection for the real malware.
---------------
How to see your datas back
For the moment i'm really bored to write a asm tool for recover your xored datas (sorry guys) so i'l leave you a pack, a free xor calculator and a free hexadecimal editor, with that you can recover your files manually.
Here you have a header of a JPG, and those who know the header will clearly reconize there is a problem on the first byte:
'B4' here is the first byte of the file, and also a victim of the xor ransomware.
The ransomware XOR all your files with 4B, so do the same operation.
XOR yourself the first byte of your damaged file with 4B
Do that for all your file, the first byte XOR 4B
Here we have the original byte: FF, now save your image and check.
Okay you have some imperfection on the image now, but that not your fault, and the file work again.
Repeat the operation in the files you need.
Click here for download
Archive password: xylibox
Your Antivirus can says calculator.exe is infected due to the wierd packer used but the file is safe ;)
This packaged contain this:
---
Edit 26 Apr 2k11: xddd.66ghz.com is now suspended (:













Intéressant ma foi ;)
ReplyDelete"PE Header of a JPG file"
ReplyDeleteCoquille ? ;)
yep, thanks (:
ReplyDeleteWhen I try to dowload:
ReplyDeleteErreur 503 - Service indisponible