Login:
Table check:
Дорогие клиенты в связи с падением пробива на эксплойтах вы вынужденны поднять цену! Цена теперь 0.6
Приношу мои извинения что так получилось, но меня заставляет рынок!
И еще правила возврата я всем объяснял не раз , возврашем тока чек которые у меня возвращается если его потом с наливаем резкий лок акк будет теперь ! Есть много людей кто идет без возвратов вообще , вот я оставлю только таких людей заранее предупреждаю.
Translate (thanks @Malwageddon):Приношу мои извинения что так получилось, но меня заставляет рынок!
И еще правила возврата я всем объяснял не раз , возврашем тока чек которые у меня возвращается если его потом с наливаем резкий лок акк будет теперь ! Есть много людей кто идет без возвратов вообще , вот я оставлю только таких людей заранее предупреждаю.
Dear customers,
Due to low callback volumes on the exploits we have to raise the price bar!
The price is now 0.6. My sincere apologies, but the current market leaves
me no choice!
And one more thing, I have explained the return policy many times now - we
only return checks that return to me. If you cash it out your account will
be locked immediately. I have many people who do not have any returns, I
think I'll be only working with these people going forward - giving you
warning in advance.
Due to low callback volumes on the exploits we have to raise the price bar!
The price is now 0.6. My sincere apologies, but the current market leaves
me no choice!
And one more thing, I have explained the return policy many times now - we
only return checks that return to me. If you cash it out your account will
be locked immediately. I have many people who do not have any returns, I
think I'll be only working with these people going forward - giving you
warning in advance.
My check:
Logs:
var_dump() mode:
We tell us some interesting query like:
select * from users where id = 8
select * from checks where user_id = 8 and validated=3
select count(*) c, sum(amount) a from checks where user_id=0 and validated=2 order by id desc limit 1000
select count(*) c from checks where user_id=0 and validated=0 order by id desc limit 1000
select * from checks where user_id=0 and validated=2 order by dt desc limit 1000
select * from log where user_id=8 order by id desc limit 1000
#!/usr/bin/php SQL:select `check`, count(*) c, min(id) m from checks group by `check` having c > 1 order by c
select * from checks where user_id = 8 and validated=3
select count(*) c, sum(amount) a from checks where user_id=0 and validated=2 order by id desc limit 1000
select count(*) c from checks where user_id=0 and validated=0 order by id desc limit 1000
select * from checks where user_id=0 and validated=2 order by dt desc limit 1000
select * from log where user_id=8 order by id desc limit 1000
#!/usr/bin/php SQL:select `check`, count(*) c, min(id) m from checks group by `check` having c > 1 order by c
https://www.betamerica.com/login_simple.jsp
proxy:socks://**.***.***.224:29583
Meisbatman:******
proxy:socks://**.***.***.224:29583
Meisbatman:******
betamerica.com is an online gambling site, they probably use this service to launder money:
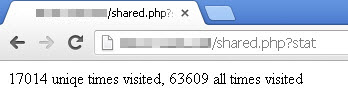
History:
Pony: