And knowing this, i was interested to crawl more panels but then i realised something...
Why did i look only for BlackPOS, instead of targeting everything ?
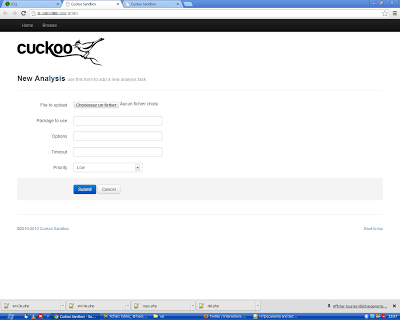
So i downloaded a random malware pack found on internet and send everything to Cuckoo.
After i've just parsed each of these generated pcaps to get some stuff (simple but effective)
Everything automated of course, it's too enormous to do that manually, especially on malware pack.
Cuckoo.
pcap junkie.
Here is a small part:
ftp://u479622:y6yf2023@212.46.196.140 - Win32/Usteal
ftp://4bf3-cheats:hydsaww56785678@193.109.247.80 - Win32/Usteal
ftp://u445497390:090171qq@31.170.164.56 - Win32/Usteal
ftp://raprap8:9Y7cGxOW@89.108.68.81 - Win32/Usteal
ftp://u195253707:1997qwerty@31.170.165.230 - Win32/Usteal
ftp://pronzo_615:f4690x0nq8@91.223.216.18 - Win32/Usteal
ftp://lordben8:xCoMFM2c@89.108.68.89 - Win32/Usteal
ftp://u698037800:denisok1177@31.170.165.251 - Win32/Usteal
ftp://u268995895:vovamolkov123@31.170.165.187 - Win32/Usteal
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.gen!A
ftp://oiadoce:cremado33@187.17.122.141 - Win32/Delf.P
ftp://cotuno:nokia400@198.23.57.29 - Win32/SecurityXploded.A
ftp://fake01:13758@81.177.6.51 - WS.Reputation.1
ftp://h51694:2222559@91.227.16.13 - Win32/Usteal
ftp://fintzet5@mail.ru:856cc58e698f@93.189.41.96 - Win32/Usteal
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Usteal
ftp://h51694:2222559@91.227.16.13 - Win32/Ganelp.E
ftp://450857:6a5124c7@83.125.22.167 - Win32/Ganelp.gen!A
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.gen!A
ftp://getmac:8F4ODYLQlvpjjQ==@222.35.250.56 - Win32/Ganelp.G
ftp://u797638036:951753zx@31.170.165.29 - Virus.Downloader.Rozena
ftp://b12_8082975:djdf3549384@10.0.2.15 - Win32/Ganelp.gen!A
ftp://onthelinux:741852abc@209.202.252.54 - Win32/Ganelp.E
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.E
ftp://450857:6a5124c7@83.125.22.167 - Win32/Ganelp.gen!A
ftp://u206748555:as3515789@31.170.165.165 - Win32/Usteal
ftp://fintzet5@mail.ru:856cc58e698f@93.189.41.96 - Win32/Usteal
ftp://griptoloji:3INULAX@46.16.168.174 - Win32/Usteal
ftp://u459704296:ded7753191ded@31.170.164.244 - Win32/Usteal
ftp://dedmen2:reaper24chef@176.9.52.231 - Win32/Usteal
ftp://srv35913:JLN18Hp7@78.110.50.123 - F*ck this shit
ftp://ftp1970492:ziemniak123@213.202.225.201 - F*ck this shit
ftp://dron2258:NRm8CNfW@89.108.68.89 - F*ck this shit
ftp://u996543000:123456789a@31.170.165.235 - F*ck this shit
ftp://u500739002:jd7H2ni99s@31.170.165.199 - F*ck this shit
ftp://0dmaer:1780199d@193.109.247.83 - F*ck this shit
ftp://u404100999:vardan123@31.170.164.25 - F*ck this shit
ftp://a9951823:www.ry123456@31.170.161.56 - F*ck this shit
ftp://u194291799:80997171405@31.170.165.18 - F*ck this shit
ftp://u478149:qqgclnbi@212.46.196.140 - F*ck this shit
ftp://u114972719:1052483w@31.170.165.192 - F*ck this shit
ftp://a1954396:omeromer123@31.170.162.103 - F*ck this shit
ftp://googgle.ueuo.com:741852@5.9.82.27 - F*ck this shit
ftp://fr32920:Nw3hRUme@92.53.98.21 - F*ck this shit
ftp://u974422848.root:vertrigo@31.170.164.119 - F*ck this shit
ftp://u205783311:gomogej200897z@31.170.165.192 - F*ck this shit
ftp://u188483768:andrewbogdanov1@31.170.165.251 - F*ck this shit
ftp://coinmint@coinslut.com:c01nm1nt!@108.170.30.2 - F*ck this shit
ftp://agooga:nokiamarco@198.23.57.29 - F*ck this shit
ftp://nicusn:n0305441@198.23.57.29 - F*ck this shit
ftp://u355595964:xmNmK4CfvX@31.170.165.193 - F*ck this shit
ftp://fmstu421:oxjQG1i7@46.4.94.180 - F*ck this shit
ftp://u651787226:123698745s@31.170.164.98 - F*ck this shit
ftp://u492312765:530021354@31.170.165.250 - F*ck this shit
ftp://mandaryn:m0jak0chanaania@213.180.150.18 - F*ck this shit
ftp://spechos8:onxGoTDG@89.108.68.85 - F*ck this shit
ftp://6fidaini:vardan123@193.109.247.80 - F*ck this shit
ftp://8steamsell:frozenn1@195.216.243.45 - F*ck this shit
ftp://u478644:57zw1q56@212.46.196.138 - F*ck this shit
ftp://u478230:lytlz3ub@212.46.196.133 - F*ck this shit
ftp://u730739228:warhammer3@31.170.165.238 - F*ck this shit
ftp://sme8:y6kByIZA@89.108.68.85 - F*ck this shit
ftp://koctbijib1@mail.ru:83670bb9072b@93.189.41.100 - F*ck this shit
ftp://u457127536:741852963q@31.170.165.245 - F*ck this shit
ftp://u450728967:987456987@31.170.165.187 - F*ck this shit
ftp://u730739228:warhammer3@31.170.165.238 - F*ck this shit
ftp://0lineage2-world:plokijuh@195.216.243.7 - F*ck this shit
ftp://expox@1:0628262733Y@188.40.138.148 - F*ck this shit
ftp://admin@enhanceviews.elementfx.com:123456@198.91.81.3 - F*ck this shit
ftp://ih_3676461:123456@209.190.85.253 - F*ck this shit
ftp://0alfa-go-cs:killer2612@195.216.243.45 - F*ck this shit
ftp://5nudapac:nudapac@195.216.243.82 - F*ck this shit
ftp://450857:6a5124c7@83.125.22.167 - F*ck this shit
I've added signature manually by browsing VirusTotal report but i got too many results so i've just leaved 'F*ck this shit' to all of them.ftp://4bf3-cheats:hydsaww56785678@193.109.247.80 - Win32/Usteal
ftp://u445497390:090171qq@31.170.164.56 - Win32/Usteal
ftp://raprap8:9Y7cGxOW@89.108.68.81 - Win32/Usteal
ftp://u195253707:1997qwerty@31.170.165.230 - Win32/Usteal
ftp://pronzo_615:f4690x0nq8@91.223.216.18 - Win32/Usteal
ftp://lordben8:xCoMFM2c@89.108.68.89 - Win32/Usteal
ftp://u698037800:denisok1177@31.170.165.251 - Win32/Usteal
ftp://u268995895:vovamolkov123@31.170.165.187 - Win32/Usteal
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.gen!A
ftp://oiadoce:cremado33@187.17.122.141 - Win32/Delf.P
ftp://cotuno:nokia400@198.23.57.29 - Win32/SecurityXploded.A
ftp://fake01:13758@81.177.6.51 - WS.Reputation.1
ftp://h51694:2222559@91.227.16.13 - Win32/Usteal
ftp://fintzet5@mail.ru:856cc58e698f@93.189.41.96 - Win32/Usteal
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Usteal
ftp://h51694:2222559@91.227.16.13 - Win32/Ganelp.E
ftp://450857:6a5124c7@83.125.22.167 - Win32/Ganelp.gen!A
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.gen!A
ftp://getmac:8F4ODYLQlvpjjQ==@222.35.250.56 - Win32/Ganelp.G
ftp://u797638036:951753zx@31.170.165.29 - Virus.Downloader.Rozena
ftp://b12_8082975:djdf3549384@10.0.2.15 - Win32/Ganelp.gen!A
ftp://onthelinux:741852abc@209.202.252.54 - Win32/Ganelp.E
ftp://b12_8082975:951753zx@209.190.85.253 - Win32/Ganelp.E
ftp://450857:6a5124c7@83.125.22.167 - Win32/Ganelp.gen!A
ftp://u206748555:as3515789@31.170.165.165 - Win32/Usteal
ftp://fintzet5@mail.ru:856cc58e698f@93.189.41.96 - Win32/Usteal
ftp://griptoloji:3INULAX@46.16.168.174 - Win32/Usteal
ftp://u459704296:ded7753191ded@31.170.164.244 - Win32/Usteal
ftp://dedmen2:reaper24chef@176.9.52.231 - Win32/Usteal
ftp://srv35913:JLN18Hp7@78.110.50.123 - F*ck this shit
ftp://ftp1970492:ziemniak123@213.202.225.201 - F*ck this shit
ftp://dron2258:NRm8CNfW@89.108.68.89 - F*ck this shit
ftp://u996543000:123456789a@31.170.165.235 - F*ck this shit
ftp://u500739002:jd7H2ni99s@31.170.165.199 - F*ck this shit
ftp://0dmaer:1780199d@193.109.247.83 - F*ck this shit
ftp://u404100999:vardan123@31.170.164.25 - F*ck this shit
ftp://a9951823:www.ry123456@31.170.161.56 - F*ck this shit
ftp://u194291799:80997171405@31.170.165.18 - F*ck this shit
ftp://u478149:qqgclnbi@212.46.196.140 - F*ck this shit
ftp://u114972719:1052483w@31.170.165.192 - F*ck this shit
ftp://a1954396:omeromer123@31.170.162.103 - F*ck this shit
ftp://googgle.ueuo.com:741852@5.9.82.27 - F*ck this shit
ftp://fr32920:Nw3hRUme@92.53.98.21 - F*ck this shit
ftp://u974422848.root:vertrigo@31.170.164.119 - F*ck this shit
ftp://u205783311:gomogej200897z@31.170.165.192 - F*ck this shit
ftp://u188483768:andrewbogdanov1@31.170.165.251 - F*ck this shit
ftp://coinmint@coinslut.com:c01nm1nt!@108.170.30.2 - F*ck this shit
ftp://agooga:nokiamarco@198.23.57.29 - F*ck this shit
ftp://nicusn:n0305441@198.23.57.29 - F*ck this shit
ftp://u355595964:xmNmK4CfvX@31.170.165.193 - F*ck this shit
ftp://fmstu421:oxjQG1i7@46.4.94.180 - F*ck this shit
ftp://u651787226:123698745s@31.170.164.98 - F*ck this shit
ftp://u492312765:530021354@31.170.165.250 - F*ck this shit
ftp://mandaryn:m0jak0chanaania@213.180.150.18 - F*ck this shit
ftp://spechos8:onxGoTDG@89.108.68.85 - F*ck this shit
ftp://6fidaini:vardan123@193.109.247.80 - F*ck this shit
ftp://8steamsell:frozenn1@195.216.243.45 - F*ck this shit
ftp://u478644:57zw1q56@212.46.196.138 - F*ck this shit
ftp://u478230:lytlz3ub@212.46.196.133 - F*ck this shit
ftp://u730739228:warhammer3@31.170.165.238 - F*ck this shit
ftp://sme8:y6kByIZA@89.108.68.85 - F*ck this shit
ftp://koctbijib1@mail.ru:83670bb9072b@93.189.41.100 - F*ck this shit
ftp://u457127536:741852963q@31.170.165.245 - F*ck this shit
ftp://u450728967:987456987@31.170.165.187 - F*ck this shit
ftp://u730739228:warhammer3@31.170.165.238 - F*ck this shit
ftp://0lineage2-world:plokijuh@195.216.243.7 - F*ck this shit
ftp://expox@1:0628262733Y@188.40.138.148 - F*ck this shit
ftp://admin@enhanceviews.elementfx.com:123456@198.91.81.3 - F*ck this shit
ftp://ih_3676461:123456@209.190.85.253 - F*ck this shit
ftp://0alfa-go-cs:killer2612@195.216.243.45 - F*ck this shit
ftp://5nudapac:nudapac@195.216.243.82 - F*ck this shit
ftp://450857:6a5124c7@83.125.22.167 - F*ck this shit
Crawling VirusTotal with the API can be also an idea to retrieve results but i'm lazy.
Looking at random pcap i've found some was fun:
Malware using free hosting service is a bad idea:
Malware builded with wrong datas (epic failure)
Malware badly coded:
Infecting yourself with Ardamax and enabling all features on it is a bad idea:
Another configuration failure:
FTP's full of sh*t:
You can learn about actors, eg from dedmen2@176.9.52.231, emo boy (i've included him on the ftp list):
Protip: don't buy a Nikon Coolpix L14v1.0, low quality picture.
I got also some false positive, this one is fun because it's a server against malware infection:
I have no idea why UsbFix was on a malware pack, anyway the use of FTP protocol for legit tools is also a bad idea, and this is not the only 'anti-malware' server i've found, got some weird stuff for viral update and many others, this technic is a double edged sword but most of result lead on malware servers.









Have you found any citadel and zeus game over in the wild?
ReplyDeletethey include the fixes to block out other malware...
ReplyDeletesoftware that record your videos? name
ReplyDeletej don't get it. All of this Ftp are allmost clear or have a few dumps of data (.bin probalby from Usteal). Most of them are random rubish or websites. Some doesn't have any malware data so why the hell did you publish some private fps with login and passwords?And why they are called malware servers?
ReplyDeleteIt's all a free FTP server's ore hacked ftp servres.
ReplyDeleteAll malware report must be encrypted. In some timout botmaster take and delete new report from server.
Botmaster don't need buy a server for report! It's dont a bug it's a feature ^)
Ahahahaha owned!!!
ReplyDeleteHeh. Somebody is trying to frame Glavmed in the ftp credentials
ReplyDelete